An OPSEC Guide to Publishing on Nostr
- Part One: Foundations of Operational Security for Decentralized Journalism
- 1. The Paradox of Platform Journalism
- 2. Threat Modeling: The Foundation of OPSEC
- 3. Foundational Principles of Digital OPSEC
- 4. Hardware Foundations for Sovereign Publishing
- 5. Identity on Nostr: Cryptographic Self-Sovereignty
- 6. Network-Level OPSEC
- 7. Communication Security
- 8. Daily OPSEC Habits
- 9. Sovereignty Requires Responsibility
- References
Part One: Foundations of Operational Security for Decentralized Journalism
Objective
This paper examines the operational security (OPSEC) requirements for journalists transitioning from centralized platforms to decentralized publishing infrastructure. As platform dependency creates single points of failure for press freedom, Nostr (Notes and Other Stuff Transmitted by Relays) emerges as a protocol-level alternative that returns control of identity, content, and monetization to individual journalists. However, technological sovereignty introduces new threat surfaces that require systematic OPSEC practices. This guide provides a threat-model agnostic framework for establishing secure publishing operations, with emphasis on the principle that security is a process, not a product.
1. The Paradox of Platform Journalism
The modern journalist faces a fundamental contradiction. The tools for global distribution have never been more accessible, yet the platforms providing this access have never been more precarious. Algorithms change without notice. Accounts are suspended without appeal. Entire publications are de-platformed at corporate discretion. The relationship between journalist and audience is mediated by interests that can sever the connection at any moment.
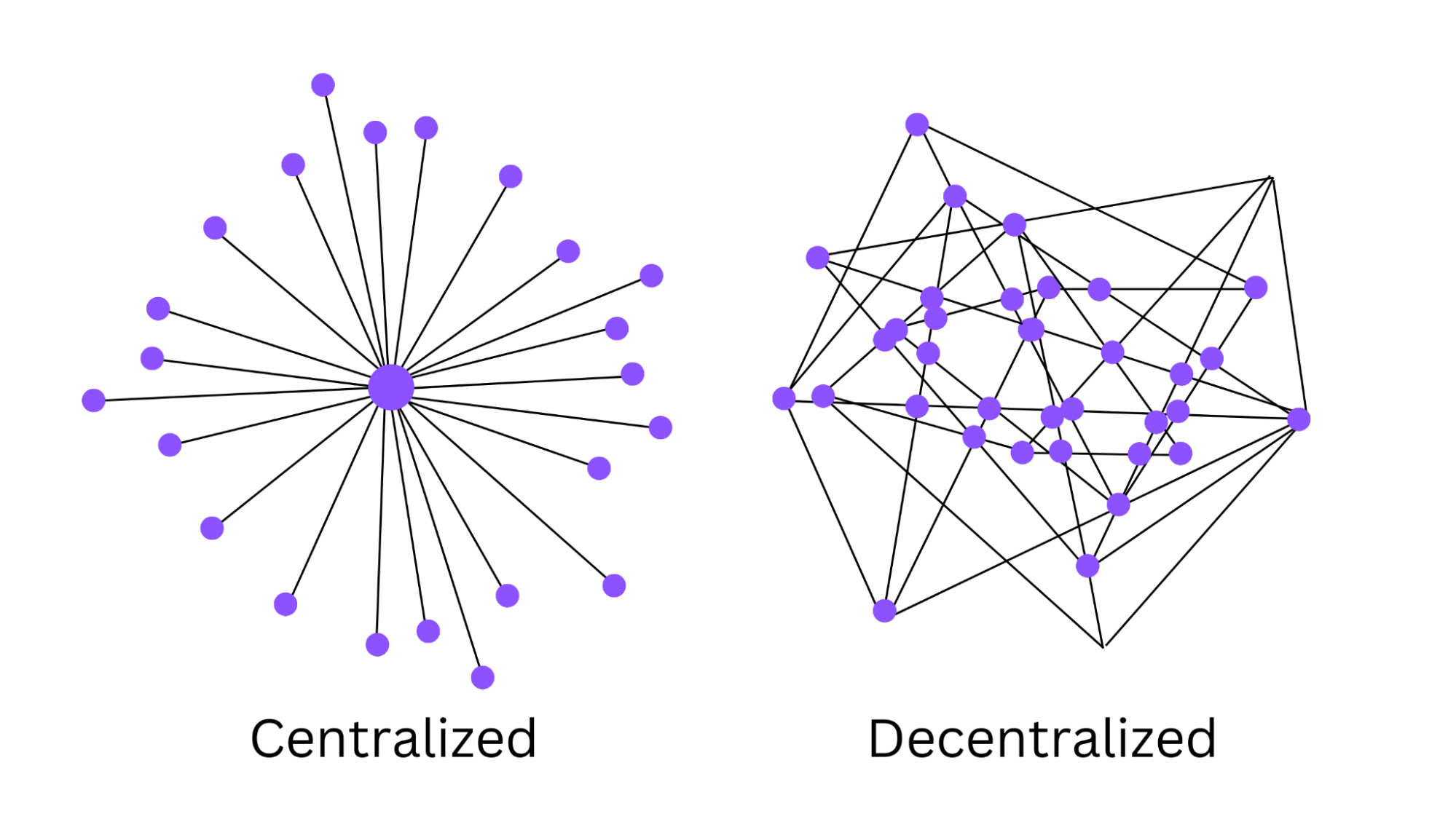
This dependency creates what security researchers call a single point of failure—a centralized choke point that can be exploited by adversaries ranging from hostile governments to corporate stakeholders. For journalists operating in the public interest, this is not merely inconvenient; it is existentially threatening to the practice of independent journalism.
Nostr offers a protocol-level alternative. By decoupling identity from infrastructure and distribution from discovery, it enables journalists to establish persistent, verifiable presence independent of any platform. But with this sovereignty comes responsibility. When you control your own keys, you bear absolute responsibility for protecting them. When you run your own infrastructure, you become responsible for its security.
This guide provides the foundational OPSEC framework for journalists adopting Nostr. It assumes you are not trying to hide from nation-state surveillance, but rather seeking to make yourself a harder target for data brokers, stalkers, platform executives, and opportunistic adversaries. It emphasizes that technology alone is insufficient—security requires mindset, habits, and systematic practice.
2. Threat Modeling: The Foundation of OPSEC
2.1 Why Threat Models Matter
Operational security is not about paranoia—it is about probability. Every digital action generates data and predictability. The more predictable you are, the easier you become to profile, track, influence, or silence.
Before implementing any security measure, you must answer a fundamental question: Who are you protecting against, and what are they capable of?
This is your threat model. It determines which precautions are necessary and which are merely performative. Security theater—installing Tor to check Facebook—wastes time and creates false confidence. Real security requires threat-specific countermeasures.
2.2 Common Threat Vectors for Journalists
Data Brokers and Advertisers: These actors aggregate behavioral data for profiling and targeting. Their methods include cross-site tracking, device fingerprinting, and data brokerage. They are pervasive but generally lack coercive power.
Platform Executives and Moderators: These actors can suspend accounts, remove content, and restrict reach. Their power is absolute within their platforms but does not extend beyond them.
Corporate and Political Adversaries: These actors may deploy legal pressure, surveillance, or social engineering to compromise sources or discredit reporting. Their capabilities vary widely but often include access to legal process and private investigation resources.
State-Level Actors: These actors possess surveillance infrastructure, legal coercion, and physical access capabilities. They are the most formidable threat and require correspondingly robust countermeasures.
Opportunistic Attackers: These actors exploit weak security for financial gain or notoriety. They are technically unsophisticated but numerous.
2.3 The Personal Threat Model
Your threats probably aren’t hackers in hoodies. They’re employers snooping, advertisers building profiles, authorities asking for metadata, stalkers, or AI scraping your digital trail. Act accordingly.
For most journalists, the goal is not perfect anonymity but sufficient opacity—making yourself expensive enough to surveil that adversaries move on to softer targets.
3. Foundational Principles of Digital OPSEC
3.1 Don’t Trust—Verify
Every person, app, network, and company must be treated as a potential leak. Not because they’re evil, but because they’re not you. They won’t lose sleep when your information gets exposed.
Default to skepticism. Ask constantly:
- Is this connection encrypted?
- Is this app open source?
- Has this software been audited?
- What data does this service collect?
- Who has access to that data?
- What happens if they’re compromised?
3.2 Everything You Share Is Permanent
Messages get screen-capped. Emails get forwarded. Cloud backups get subpoenaed. If it’s digital, it’s duplicable. If it’s duplicable, it’s uncontrollable.
This principle has two implications: First, think carefully before creating any digital artifact. Second, assume that anything you create will eventually become public and plan accordingly.
3.3 Anonymity Dies in Cross-Reference
You use the same username on different platforms? You’re already deanonymized. You check Telegram from the same IP you use for banking? Done. Your habits are the fingerprint.
Adversaries rarely need to crack encryption. They simply correlate identifiers across contexts until identity emerges. The solution is strict compartmentalization—different identifiers for different roles, never crossing streams.
3.4 Metadata Is More Dangerous Than Content
What you said matters less than when, where, and to whom. Call logs reveal more than call audio. Message timing reveals more than message content. Location pings reveal more than social posts.
Encryption protects content but often leaves metadata exposed. Encrypt the payload, but also obscure the headers when possible. For journalists, the fact that you’re communicating with a source may be more sensitive than the content of the communication.
3.5 The Perfection Fallacy
You don’t have to be perfect. You just have to be less predictable than the next target. Make surveillance harder, more expensive, more uncertain.
Security is not binary. Every improvement reduces risk. Do not abandon security because you cannot achieve perfection.
4. Hardware Foundations for Sovereign Publishing
4.1 Hardware as a Trust Anchor
Software can be audited, patched, and replaced. Hardware is the physical root of trust. If your hardware is compromised, nothing running on it can be trusted.
This reality has profound implications: the device you use for journalism must be treated as a trust anchor. Its supply chain, physical security, and operational integrity determine the security of everything above it.
4.2 The Entry Point: Repurposed Chromebook
You don’t need expensive gear to start. A used Chromebook from 2017-2019 can be acquired for approximately $59. Models like the Acer Chromebook R11 (Celeron N3150, 4GB RAM), Dell Chromebook 11 3180 (Celeron N3060, 4GB RAM), or HP Chromebook 11 G5 (Celeron N3350, 4GB RAM) are frequently available at this price point.
After installing Linux (via MrChromebox firmware or Crouton), this machine can run basic Nostr infrastructure, handle key management, and serve as a dedicated journalism device. Limitations include slower I/O and limited RAM, making it unsuitable for high-traffic operations. It is, however, an excellent learning platform and a true “burner laptop” for compartmentalized work.
OPSEC Advantages:
- Low cost enables true compartmentalization
- Limited functionality reduces attack surface
- Repurposed hardware has no manufacturer backdoors (unlike new consumer devices)
- Easily replaced if compromised
4.3 The Professional Rig: AMD NUC
For production use, an AMD-based NUC form factor provides the ideal balance of power efficiency and computational capacity. Recommended specifications:
- Model: Minisforum UM250 or UM350 (AMD Ryzen 5)
- RAM: 16GB DDR4 (minimum)
- Storage: 512GB NVMe SSD
- Network: Gigabit Ethernet
- Cost: Approximately $350-500 for the barebones unit
These systems draw only 15-25 watts—quiet enough for a home office, efficient enough to run 24/7. The AMD chips include AES-NI support, accelerating encryption operations.
OPSEC Advantages:
- Hardware-accelerated encryption
- Sufficient resources for full-stack operations
- Small form factor enables physical concealment
- Commercial supply chain reduces targeting risk
4.4 Physical Security Essentials
Whichever hardware you choose:
Full Disk Encryption is non-negotiable. If someone steals your machine, they should find nothing but scrambled bits. LUKS for Linux, BitLocker for Windows, FileVault for macOS—all are acceptable when properly configured with strong passphrases.
BIOS Passwords prevent booting from attacker-controlled media. Set a supervisor password and disable boot from external devices.
Tamper-Evident Seals on case seams alert you to physical intrusion. Cheap holographic stickers make removal obvious.
Lockable Port Doors block “evil maid” attacks via USB devices. Physical access is total access; prevent it when possible.
Separate Power Supplies for your journalism devices. Never plug them into unknown USB ports, which can deliver data exfiltration attacks.
Secure Disposal Protocols for retired hardware. Physical destruction or multiple overwrites prevent data recovery.
5. Identity on Nostr: Cryptographic Self-Sovereignty
5.1 The Npub and the Nsec
Your Nostr public key (npub) is your permanent identity—share it freely. It is a cryptographic identifier that cannot be impersonated without access to your private key.
Your private key (nsec) is your lifeblood. If it’s compromised, everything attached to it is compromised. There’s no “reset password” button. No customer support to call. No recovery mechanism.
This is simultaneously Nostr’s greatest strength and greatest danger. You control your identity absolutely—but you also bear absolute responsibility for protecting it.
5.2 Key Management Principles
Never type your nsec into random apps. Applications should never see your key. Use event signers that hold the key and request signature approval.
Never paste it into websites. Web forms are exfiltration vectors. Any site asking for your nsec is malicious or incompetent.
Never store it in cloud services. Cloud backups are accessible to cloud providers, governments, and attackers.
Never take screenshots of it. Screenshots are automatically backed up, indexed, and potentially leaked.
Never email it to yourself. Email is transmitted in plaintext between servers and stored indefinitely.
5.3 Event Signers: The Safe Compromise
Event signers are tools that hold your key and sign events without exposing the key to applications. They represent the difference between handing someone your credit card versus approving individual charges.
Amber (Android): Acts as a system-wide signer, keeping your nsec isolated from apps. Applications request signatures; Amber prompts you to approve. The key never leaves Amber’s secure storage.
nos2x (Browser extension): Signs events from web clients without exposing the key. The extension holds your key; websites request signatures.
Alby (Browser extension): Combines Lightning wallet and Nostr signer functionality. Holds your key and manages both payments and identity.
Even these tools haven’t undergone formal security audits, but they’re vastly safer than pasting your key everywhere. They represent the current best practice for daily Nostr use.
5.4 Compartmentalization Strategies
Different Keys for Different Roles: Your journalism identity should not share keys with your experimental Nostr account, your source communication identity, or your personal presence. Use separate key pairs for each role.
Master Key and Publishing Keys: Generate a master key held in cold storage. Generate a separate publishing key for daily use. If the publishing key is compromised, you can revoke it and attest to the new key with your master key.
Source-Specific Keys: For highly sensitive sources, generate unique key pairs. Compartmentalization limits damage if any single key is compromised.
5.5 The Parent/Child Problem
Currently, Nostr lacks a proper hierarchical key system. There’s no way to generate child keys with limited permissions that can be revoked if compromised. This is especially dangerous for journalists who might outsource social media management—a disgruntled former employee with your nsec can destroy your identity permanently.
Until this improves, treat your nsec with extreme prejudice. It touches only dedicated, airgapped, never-online hardware when possible.
5.6 Key Generation and Backup
Generation: Generate keys offline, on a machine that has never been and will never be networked. Use trusted, open-source tools. Verify the software you’re using.
Storage: Store seed phrases on metal (stamped into titanium or steel), not paper. Metal survives fire, flood, and decay. Store in a physically secure location separate from your primary device.
Backup: Create multiple copies of the seed phrase, stored in geographically separate locations. Consider a safety deposit box for one copy.
Verification: After backup, verify that you can restore from the seed phrase on a different device. Test your recovery process before you need it.
6. Network-Level OPSEC
6.1 IP Address as Identifier
Your IP address is a persistent identifier that can be correlated across contexts. It reveals your approximate location, your ISP, and potentially your identity.
For journalists, IP exposure means:
- Relay operators can log your activity
- Adversaries can correlate your Nostr usage with other online activity
- Legal process can compel ISPs to identify you
6.2 Mitigation Strategies
VPNs: A trustworthy VPN hides your IP from relays and other services. Choose a VPN that:
- Accepts anonymous payment (cash, Bitcoin)
- Has a verified no-logs policy
- Is based in a jurisdiction favorable to privacy
- Uses strong encryption
Tor: The Tor network routes traffic through multiple relays, hiding your IP from destination servers. Tor is slower than VPNs but provides stronger anonymity when used correctly.
Mixed Approaches: Connect to your personal relays over clearnet (fast, controlled by you). Route all other Nostr traffic through Tor or VPN. This balances performance with privacy.
Important Warning: Run VPN over Tor, not Tor over VPN. VPN through Tor protects you from malicious exit nodes. Tor through VPN exposes you to VPN logging.
6.3 DNS Leakage
DNS queries reveal every domain you visit. Even if you use a VPN, DNS requests may leak outside the encrypted tunnel if not properly configured.
Solutions:
- Use VPNs with built-in DNS leak protection
- Configure DNS to use encrypted protocols (DNS-over-HTTPS, DNS-over-TLS)
- Use DNS providers that don’t log (NextDNS with hardened settings)
6.4 Browser Fingerprinting
Even with IP hidden, browsers reveal extensive identifying information: screen resolution, installed fonts, browser extensions, timezone, language preferences. This combination often uniquely identifies users.
Mitigations:
- Use privacy-respecting browsers (Brave, Firefox with strict settings, Mull on Android)
- Install uBlock Origin in medium mode
- Use Canvas Blocker to prevent fingerprinting
- Disable JavaScript when possible
- Use different browser profiles for different contexts
7. Communication Security
7.1 The DM Problem on Nostr
Basic Nostr direct messages (kind 4) encrypt content but leave metadata exposed. Anyone with access to relays can see:
- Who is messaging whom
- Timestamps of messages
- Approximate message sizes
- Frequency of communication
This metadata can be as revealing as content. Communication patterns reveal relationships, schedules, and priorities.
7.2 Gift Wrapping (NIP-59)
NIP-59 “gift wrapping” adds three layers of encryption that obscure metadata:
- The message is encrypted for the recipient
- The encrypted message is placed inside another encrypted envelope
- The wrapped message is delivered through relays that see only ciphertext
Relays see only that someone sent an encrypted message to someone else—not who the real participants are. This provides Signal-level privacy, but with the crucial difference that you control your keys.
7.3 Secure Clients
0xChat leads the pack for secure messaging. Built specifically around privacy, it implements:
- NIP-59 gift wrapping by default
- Built-in Cashu wallet for private payments
- Private groups with encrypted membership
- No metadata exposure
Amethyst (Android) allows configuring Tor for non-trusted relays. Your trusted relays connect over clearnet for speed; everything else routes through Tor.
7.4 Source Communication Best Practices
Never reuse identifiers: Each source should have a unique way to reach you—different email aliases, different Nostr pubkeys if possible, different Signal accounts.
Establish verification rituals: Pre-arranged code phrases. Signed messages with known keys. Video calls with specific hand gestures. Verify identity before sharing sensitive information.
Assume compromise and plan accordingly: What happens if your device is seized? If your nsec is exposed? If a source’s device is compromised? Have contingency plans.
Use dead drops for highly sensitive material: Encrypted files uploaded to anonymous locations, with retrieval instructions delivered separately.
Minimize digital artifacts: Prefer in-person meetings when possible. Use ephemeral communication channels. Delete sensitive conversations after action.
8. Daily OPSEC Habits
8.1 Digital Hygiene
Use different usernames for different roles: Social, work, crypto, political—each gets its own handle, its own email aliases, its own compartment. Cross-reference is how anonymity dies.
Turn off WiFi and Bluetooth when not using them: Your devices broadcast identifying information constantly. Stop the signal when you don’t need it.
Use privacy-respecting browsers: Brave, Firefox with strict settings, or Mull on Android. Add uBlock Origin, JavaScript blockers, and canvas fingerprinting protection.
Use DNS that doesn’t log: NextDNS with hardened settings prevents your ISP from seeing every site you visit.
Check what apps are really doing: Tools like Exodus Privacy, NetGuard, and TrackerControl reveal which apps are phoning home and to whom.
Keep software updated: Vulnerabilities are discovered constantly. Updates patch known exploits.
8.2 Compartmentalization
Separate phone for junk tasks: Ride shares, food delivery, random apps—all on a cheap secondary phone with minimal personal data.
Burner laptops for sensitive work: That $59 Chromebook becomes your journalism machine. It never touches personal accounts, never browses social media, never does anything but sovereign publishing.
Airgapped signing: For critical operations—publishing major investigations, rotating keys—use a machine that has never been online. Transfer transactions via QR codes or USB drives that have never touched the internet.
Virtual machines for risky tasks: When you must use potentially untrusted software, isolate it in a virtual machine that can be discarded after use.
8.3 Minimizing Footprint
Don’t post in real time: Delay publication. Stagger timestamps. Make correlation harder.
Don’t geotag anything: Strip metadata from photos. Assume location data reveals more than you intend.
Don’t sync everything to the cloud: Every extra bit of data in someone else’s data center is an anchor point for adversaries.
Don’t use the same devices for everything: Compartmentalization limits the damage from any single compromise.
Know when to walk away: If an app gets shady, drop it. If a service demands ID, burn it. If a platform changes terms, don’t argue—exit. You owe nothing to digital landlords.
8.4 The Security Mindset
Security is not a one-time configuration. It is a continuous practice. New threats emerge. New vulnerabilities are discovered. New tools become available.
Cultivate habits of skepticism and verification. Question assumptions. Test your security. Assume you will be compromised and plan accordingly.
9. Sovereignty Requires Responsibility
Nostr offers journalists something unprecedented: true independence from platform gatekeepers, cryptographically verifiable identity, and direct economic relationships with readers. But this sovereignty comes with responsibility.
When you control your own keys, you bear absolute responsibility for protecting them. When you run your own infrastructure, you become responsible for its security. When you communicate directly with sources, you must ensure those communications remain confidential.
The tools exist. The community exists. The protocols are mature. What remains is the willingness to adopt the mindset and habits that make security possible.
For the journalist willing to invest in their own infrastructure and their own security practices, Nostr offers a path to publishing freedom that no platform can revoke. The question is not whether the technology works—it does. The question is whether journalists will claim their sovereignty.
References
-
Schneier, B. (2015). Secrets and Lies: Digital Security in a Networked World. Wiley.
-
Nostr Protocol NIPs. Available at: https://github.com/nostr-protocol/nips
-
Electronic Frontier Foundation. (2024). Surveillance Self-Defense Guide. Available at: https://ssd.eff.org
-
Freedom of the Press Foundation. (2024). Digital Security Training for Journalists. Available at: https://freedom.press/training/
-
NIP-59: Gift Wrap. Available at: https://github.com/nostr-protocol/nips/blob/master/59.md
-
Tor Project. (2024). Tor Overview. Available at: https://torproject.org
-
Cashu Protocol Documentation. Available at: https://cashu.space
-
Rizful Security Architecture. Available at: https://rizful.com
-
0xChat Privacy Features. Available at: https://0xchat.com
-
Citizen Lab. (2023). Digital Threats to Journalists. University of Toronto.