An OPSEC Guide to Publishing on Nostr - The Sovereign Correspondent — A Technical Analysis of Nostr Infrastructure for Journalistic Independence
- 1. The Protocol: Why Nostr for Journalism?
- 2. Game Theory: Aligning Incentives in a Decentralized Network
- 3. Infrastructure Specifications: From $59 Chromebook to Production NUC
- 4. Relay Architecture: Implementing the Pyramid Model
- 5. Monetization Infrastructure: Ecash and Lightning
- 6. Identity and Key Management
- 7. Privacy and OPSEC Considerations
- 8. The Web of Trust in Practice
- 9. Source Communication: The Secure Channel
- 10. Putting It All Together: The Sovereign Journalism Stack
- 11. The Viability of Sovereign Journalism
- References
The modern journalist faces a paradox. The tools for global distribution have never been more accessible, yet the platforms that provide this access have never been more precarious. Algorithms change, accounts are suspended, entire publications are de-platformed. The relationship between journalist and audience is mediated by corporate interests that can sever the connection at any moment.
This article examines an alternative: a self-sovereign publishing infrastructure built on Nostr (Notes and Other Stuff Transmitted by Relays). We analyze the technical specifications, operational requirements, and emergent game theory of running personal relays, integrating ecash micropayments, and establishing a cryptographically-verified identity—all on commodity hardware starting at under $60.
1. The Protocol: Why Nostr for Journalism?
Nostr is not a platform but a protocol. It consists of two simple components: clients (which users interact with) and relays (which store and forward messages). Anyone can run a relay. Anyone can write a client. This decentralization is fundamental.
For a journalist, this architecture provides guarantees that centralized platforms cannot:
- Persistence: Your content exists on relays you control. If a relay operator disappears, your other relays continue serving your content.
- Verifiability: Every event is signed with your private key. Readers can cryptographically verify that you—and not an impersonator—published a given note. In an era of AI-generated disinformation, this non-repudiation is foundational.
- Portability: Your identity (your public key) is independent of any specific relay. You can change relays, add relays, or remove relays without losing your followers or your history.
The protocol does not enforce any particular economic or social model. This is where game theory enters.
2. Game Theory: Aligning Incentives in a Decentralized Network
Nostr’s design creates a unique set of incentives that, when properly understood, can be leveraged for journalistic integrity.
2.1 Relay Competition
Relays compete on features, reliability, and price. A journalist running their own relays internalizes the cost of infrastructure but gains complete control over content retention and access policies. Public relays compete to attract users by offering free storage, but they may impose limits or insert ads. The existence of the personal relay option caps the power of any single public relay.
This competitive landscape means no single entity controls the flow of information. If a public relay begins censoring content or injecting malware, journalists can simply point their clients to different relays—including their own.
2.2 The Web of Trust
Nostr enables Web of Trust (WoT) mechanisms. By analyzing who follows whom, algorithms can compute trust scores. This creates a market for reputation. A journalist who consistently publishes verified information accrues trust edges from other trusted accounts. Spammers and propagandists remain isolated from the core trust graph.
The game theory is straightforward: trust is a form of social capital that accumulates through honest behavior. It cannot be bought, only earned.
2.3 Micropayment Economics
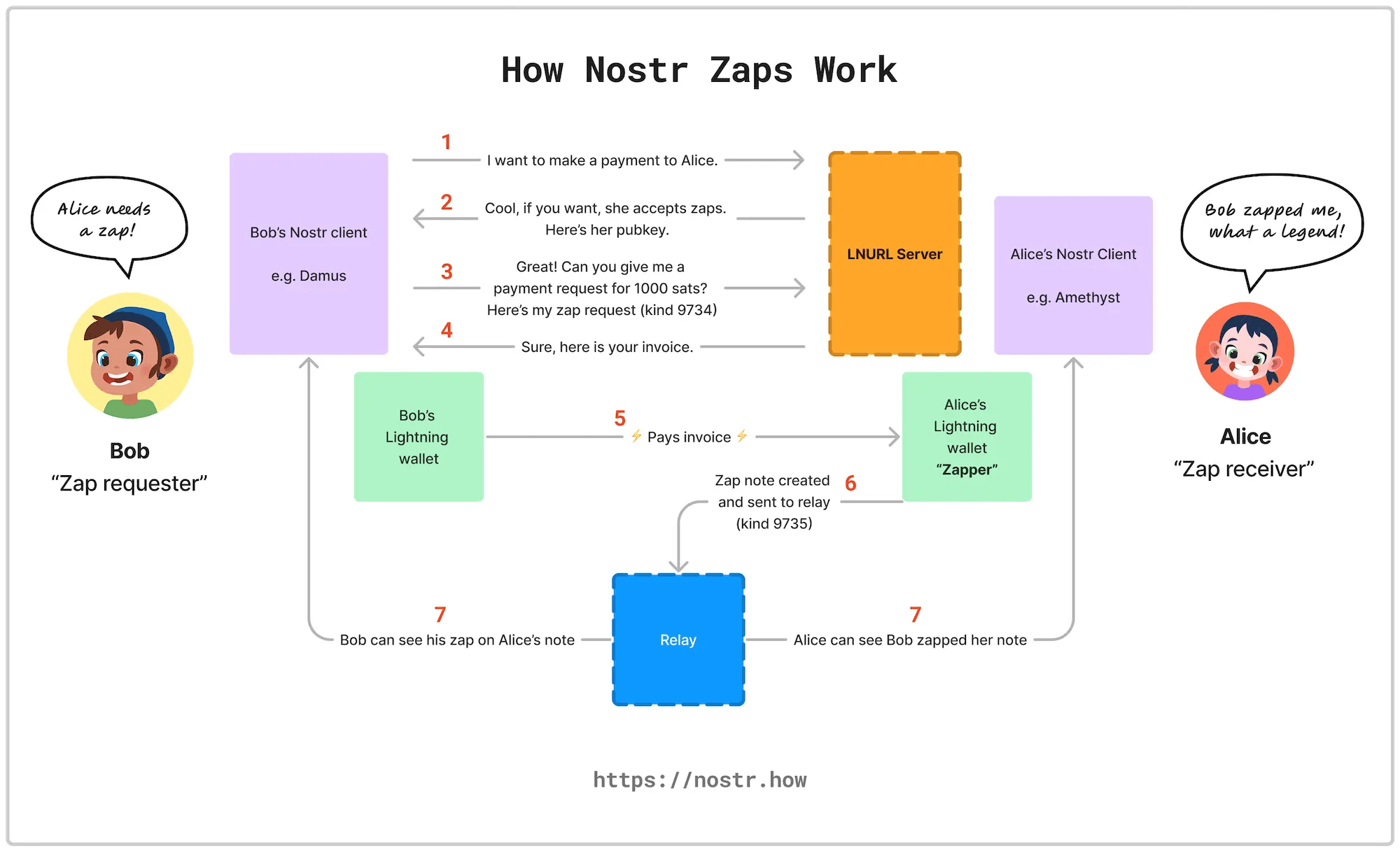
With Lightning Network integration, Nostr enables frictionless micropayments (zaps). This aligns incentives: readers can directly support journalists whose work they value, bypassing advertising models. The game theory here is pure: quality content attracts sats; low-effort or misleading content does not.
Unlike platform-based monetization (where algorithms decide who gets paid), zap economics are direct and transparent. Every sat represents a reader’s voluntary valuation of your work.
3. Infrastructure Specifications: From $59 Chromebook to Production NUC
The hardware required for a sovereign journalism stack ranges from ultra-budget experimentation to professional-grade reliability.
3.1 Entry Level: The Repurposed Chromebook
A used Chromebook from 2017-2019 can be acquired for approximately $59. Models like the Acer Chromebook R11 (Celeron N3150, 4GB RAM), Dell Chromebook 11 3180 (Celeron N3060, 4GB RAM), or HP Chromebook 11 G5 (Celeron N3350, 4GB RAM) are frequently available at this price point.
After installing Linux (via MrChromebox firmware or Crouton), this machine can run a basic Nostr relay, handle key management, and serve as a dedicated journalism device. Limitations include slower I/O and limited RAM, making it unsuitable for high-traffic relays or database-heavy operations. It is, however, an excellent learning platform and a true “burner laptop” for compartmentalized work.
OPSEC Consideration: This device should do nothing but run your journalism infrastructure. No social media scrolling. No personal email. No banking. It exists solely for your sovereign publishing stack.
3.2 Professional Grade: AMD NUC
For production use, an AMD-based NUC form factor provides the ideal balance of power efficiency and computational capacity. Recommended specifications:
- Model: Minisforum UM250 or UM350 (AMD Ryzen 5)
- RAM: 16GB DDR4 (minimum)
- Storage: 512GB NVMe SSD + optional 1TB for chain data
- Network: Gigabit Ethernet
- Cost: Approximately $350-500 for the barebones unit
These systems draw only 15-25 watts—quiet enough for a home office, efficient enough to run 24/7 without spiking your electric bill. The AMD chips include AES-NI support, accelerating the encryption operations that secure your communications.
OPSEC Consideration: Full disk encryption is non-negotiable. If someone steals your machine, they should find nothing but scrambled bits. BIOS passwords prevent booting from attacker-controlled media. Tamper-evident stickers on case seams alert you to physical intrusion.
4. Relay Architecture: Implementing the Pyramid Model
Fiatjaf’s Pyramid relay implementation embodies the concept of “communityzenship”—a relay where users participate in governance. For a journalist, running three Pyramid relays provides redundancy and ensures content availability even if any single relay experiences issues.
4.1 Relay Roles
Primary Write Relay: Accepts posts only from your key. This is your authoritative source. Others look here to find your content. Only you should be able to post to it.
Backup Relay: Mirrors your content. If the primary is unreachable or compromised, the backup serves your notes. This provides redundancy against hardware failure or network issues.
Community/Inbox Relay: Accepts replies, reactions, and DMs. Configured for NIP-17 encrypted direct messages, this relay handles source communications and reader engagement.
4.2 Operational Considerations
Each relay requires:
- A domain name or static IP
- TLS certificate (for wss:// encrypted WebSocket connections)
- Persistent storage for the event database
- Regular backups (separate from the live system)
Pyramid is written in Go, offering efficient concurrency. The database stores events; proper indexing is critical for performance. For a journalist’s personal relays, SQLite is sufficient; for high-traffic public relays, PostgreSQL is recommended.
4.3 The Outbox Model
Modern Nostr clients use the “outbox model”—different relays for different purposes. Your outbox relay (primary write) stores everything you write. Your inbox relay (community) receives replies and mentions. Your chat relay handles private messages.
This separation means that even if your community relay is compromised, your published content remains available through your primary and backup relays. If your primary relay is targeted, you can continue publishing through the backup while restoring the primary.
5. Monetization Infrastructure: Ecash and Lightning
Direct reader support requires a payments infrastructure that respects privacy and minimizes friction. Two complementary approaches serve different use cases.
5.1 Rizful: Lightning Address as a Service
Rizful provides free Lightning addresses integrated with Nostr Wallet Connect (NWC). For journalists, this means:
- A professional
@yourname.rizful.comhandle - Automatic zap handling in compatible clients
- No requirement to run your own Lightning node
- Enterprise-grade reliability (backed by The Megalith Node, one of the largest routing nodes on the Lightning Network)
Rizful’s security model separates identity from funds: your Lightning balance is protected by email and two-factor authentication, not by your Nostr private key. If your nsec is compromised, your funds remain safe. If you lose your nsec, you can recover your Rizful account through email.
How it works: Readers zap your posts through any Nostr client. The zap request goes to your Rizful Lightning address, which processes the payment and credits your account. The entire process takes less than one second due to Rizful’s central position in the Lightning Network.
OPSEC Consideration: Use a privacy-preserving email service or “hide my email” feature when signing up. Enable two-factor authentication immediately. Only keep funds you expect to use on Lightning in the near future—long-term storage belongs on a hardware wallet.
5.2 Cashu Nutshell: Running a Personal Ecash Mint
For privacy-preserving micropayments, a journalist can run their own Cashu mint using the Nutshell implementation. Cashu implements Chaumian ecash—blinded tokens that provide cryptographic privacy for both sender and receiver.
Think of it like digital cash. When a reader pays a Lightning invoice to your mint, they receive blinded tokens that only they can spend. When they send those tokens to you, you redeem them for real sats—but neither of you can see the other’s transaction history.
For journalists, this means:
- Readers can support you without exposing their identities
- You receive funds without knowing who sent them (perfect for confidential sources)
- Transactions don’t appear on public blockchains
- Tokens can be transferred offline, via airgap, or even over Nostr itself
Technical Requirements:
- Docker environment for containerized mint operation
- PostgreSQL or SQLite for database
- Redis for optional caching (NUT-19)
- Lightning node connection (LND, CLN) for backing ecash with real bitcoin
Operational Notes: The mint issues tokens backed by Lightning invoices. Readers pay an invoice, receive blinded tokens, and can spend them with you or other Cashu-compatible wallets. The mint never learns the identity of the spender.
Important Caveat: The Nutshell documentation explicitly warns that the software is experimental, unaudited, and likely contains fatal flaws. Start with trivial amounts. Consider this technology for its innovative potential rather than production readiness.
6. Identity and Key Management
The cornerstone of journalistic sovereignty is the private key (nsec). Compromise is unrecoverable. There is no “reset password” button. No customer support to call.
6.1 Key Generation and Storage
Generation: Generate keys offline, on a machine that has never been and will never be networked. Use trusted, open-source tools. Verify the software you’re using.
Storage: Store the seed phrase on metal (stamped into titanium or steel), not paper. Metal survives fire, flood, and decay. Store it in a physically secure location separate from your primary device.
Backup: Create multiple copies of the seed phrase, stored in geographically separate locations. Consider a safety deposit box for one copy.
6.2 Daily Signing
For daily signing, use an event signer application that holds the key and requests user approval for each signature. Options include:
- Amber (Android): Acts as a system-wide signer, keeping your nsec isolated from apps
- nos2x (Browser extension): Signs events from web clients without exposing the key
- Alby (Browser extension): Lightning and Nostr integration with key management
The key never touches the client application. When a client requests a signature, the signer prompts you to approve. This is the difference between handing someone your credit card versus approving individual charges.
6.3 Compartmentalization
Use different keys for different purposes:
- Master key: Extremely cold storage. Used only for identity attestations and key rotations. Touches a networked device perhaps once a year.
- Publishing key: Used for daily notes. If compromised, you can revoke it and attest to the new key with your master key.
- Source communication key: Used only for DMs with sensitive sources. If this key is compromised, your master identity remains intact.
- Test/experimental key: For trying new clients and features without risking your primary identity.
6.4 The Parent/Child Problem
Currently, Nostr lacks a proper hierarchical key system. There’s no way to generate child keys with limited permissions that can be revoked if compromised. This is especially dangerous for journalists who might outsource social media management—a disgruntled former employee with your nsec can destroy your identity permanently.
Until this improves, treat your nsec like the nuclear codes. It touches only dedicated, airgapped, never-online hardware when possible.
7. Privacy and OPSEC Considerations
7.1 Metadata Exposure
Basic Nostr DMs (kind 4) encrypt content but leave metadata visible to relays. Anyone can see:
- Who is messaging whom
- Timestamps of messages
- Approximate message sizes
- Frequency of communication
This metadata can be as revealing as content. NIP-59 (Gift Wrap) adds three layers of encryption that obscure metadata. The message is encrypted, then placed inside another encrypted envelope, then delivered through relays that see only ciphertext.
Clients like 0xChat implement this by default. For journalists handling sensitive source communications, 0xChat represents the current state of the art—Signal-level security, but you control the keys.
7.2 IP Leakage
Connecting to public relays exposes your IP address to relay operators. Solutions:
- Connect to your personal relays directly: Clearnet, but controlled by you. Your IP is visible only to your own infrastructure.
- Route connections to untrusted relays through Tor: Use Tor for any relay you don’t operate yourself.
- Use a VPN for all Nostr traffic: Choose a no-log VPN provider that accepts anonymous payment.
- Combine approaches: Personal relays over clearnet for speed; all other traffic over Tor or VPN.
7.3 Physical Security
- Full disk encryption on all devices. If it’s off, it’s unreadable.
- BIOS passwords and secure boot to prevent booting from attacker-controlled media.
- Tamper-evident seals on device cases to detect physical intrusion.
- Separate, dedicated devices for journalism work. No crossover with personal or work devices.
- Lockable port doors to prevent “evil maid” attacks via USB devices.
7.4 Digital Hygiene for Journalists
Different usernames for different roles: Your journalism identity should not share usernames with your gaming accounts, your crypto trading, or your personal social media. Cross-reference is how anonymity dies.
Burner emails for everything: Services like SimpleLogin or Firefox Relay generate disposable email aliases. Your Nostr accounts, your domain registrar, your VPS provider—all should use unique, unconnected email addresses.
Unique passwords everywhere: A password manager isn’t optional. Your master password should be long, unique, and memorized. Everything else gets randomly generated 20+ character strings.
Two-factor authentication on every service: Preferably hardware tokens (YubiKey) rather than SMS or authenticator apps, though authenticator apps are better than nothing.
Check what apps are really doing: Tools like Exodus Privacy, NetGuard, and TrackerControl reveal which apps are phoning home and to whom.
8. The Web of Trust in Practice
Reputation on Nostr is not granted by a central authority but earned through network connections. A journalist’s Web of Trust score is the aggregate of trust edges from other verified journalists, sources, and readers.
8.1 Building Trust
Publish consistently under your verified key: Every signed note adds to your history. Consistency builds credibility.
Interact with other trusted accounts: Engage with established journalists in your field. Their follows and interactions add trust edges to your graph.
Have your key signed by established journalists: GPG-style cross-signing, or via NIP-05 identifiers (verifying that your domain associates with your key).
Publish NIP-85 “Trusted Assertions” about other accounts you verify. This contributes to the ecosystem and establishes you as a trust anchor.
8.2 Using WOT for Filtering
Specialized relays like Brainstorm compute personalized trust scores. They analyze the follow graph and can filter out content from untrusted sources.
A journalist can run their own WOT relay, ensuring their feed contains only notes from accounts within their trust network. This dramatically reduces spam and disinformation while preserving the openness that makes Nostr valuable.
8.3 The Game Theory of Trust
Trust on Nostr is not abstract—it has real consequences. Accounts with high trust scores attract more followers, more engagement, and more zaps. Low-trust accounts are filtered out by WOT relays, reducing their reach.
This creates strong incentives for honest behavior. A journalist who publishes verified information builds trust capital. One who spreads disinformation loses it. The market for reputation enforces quality more effectively than any central authority.
9. Source Communication: The Secure Channel
For journalists, source protection is non-negotiable. Nostr, properly configured, can provide secure communication channels.
9.1 NIP-17 Direct Messages
NIP-17 implements “Sealed Direct Messages”—encrypted messages that hide metadata. The protocol uses:
- Gift wrapping: The message is encrypted for the recipient, then wrapped in another encrypted envelope
- Blind relays: Relays see only ciphertext, not who is communicating with whom
- Proof-of-work: Optional anti-spam mechanism
9.2 Best Practices for Source Communication
Establish verification rituals: Pre-arranged code phrases. Signed messages with known keys. Video calls with specific hand gestures. Verify identity before sharing sensitive information.
Use separate keys for different sources: If possible, generate unique key pairs for each sensitive source. Compartmentalization limits damage if any single key is compromised.
Never reuse identifiers: Each source should have a unique way to reach you—different email aliases, different Nostr pubkeys if possible, different Signal accounts.
Assume compromise and plan accordingly: What happens if your device is seized? If your nsec is exposed? If a source’s device is compromised? Have contingency plans.
Use dead drops for highly sensitive material: Encrypted files uploaded to anonymous locations, with retrieval instructions delivered separately.
9.3 0xChat: A Case Study in Secure Messaging
0xChat deserves special attention as a Nostr client built around privacy. It implements:
- NIP-59 gift wrapping by default
- Built-in Cashu wallet for private payments
- Private groups with encrypted membership
- No metadata exposure
For journalists handling sensitive communications, 0xChat represents the current state of the art—all the security of Signal, but with user-controlled keys and integrated ecash.
10. Putting It All Together: The Sovereign Journalism Stack
10.1 The Complete Infrastructure
Hardware Tier 1 (Entry): Repurposed Chromebook ($59), full disk encryption, dedicated to journalism only.
Hardware Tier 2 (Professional): AMD NUC ($350-500), 16GB RAM, NVMe storage, running 24/7.
Identity: Master key in cold storage. Publishing key for daily use. Source keys compartmentalized.
Relays: Three Pyramid relays configured for outbox/inbox/chat roles.
Monetization: Rizful Lightning address for easy tips. Personal Cashu mint for privacy-preserving ecash (experimental).
Communication: 0xChat for secure DMs with gift wrapping. Separate channels for different source tiers.
Reputation: Personal Web of Trust relay filtering content based on your network. Published trust assertions contributing to ecosystem.
Habits: Compartmentalized identities, minimal footprint, regular security reviews.
10.2 The Workflow
- Write: Compose in your preferred client, connected to your personal relays
- Publish: Notes are signed with your publishing key and stored on your three relays
- Distribute: Readers fetch content from any of your relays—redundancy ensures availability
- Monetize: Readers zap via your Rizful Lightning address; privacy-conscious readers use your Cashu mint
- Communicate: Sources reach you via encrypted DMs through your community relay
- Verify: Readers check signatures and Web of Trust scores to confirm authenticity
11. The Viability of Sovereign Journalism
The stack described—three Pyramid relays, a Rizful Lightning address, a local Cashu mint, and a Web of Trust relay—is technically feasible on hardware costing under $500. It requires no permission from any platform. It cannot be de-platformed. Its monetization is direct, private, and uncensorable.
The game theory is elegant: journalists who serve their audience well are rewarded with sats and trust edges. Those who don’t are ignored. The protocol itself enforces no penalties, but the emergent social and economic dynamics create strong incentives for integrity.
For the journalist willing to invest in their own infrastructure, Nostr offers something unprecedented: true independence, cryptographically verifiable identity, and a direct economic relationship with readers.
The tools exist. The community exists. The question is whether journalists will claim their sovereignty.
References
- Nostr Protocol NIPs. Available at: https://github.com/nostr-protocol/nips
- Pyramid Relay GitHub Repository. fiatjaf. Available at: https://github.com/fiatjaf/pyramid
- Cashu Nutshell: Chaumian Ecash Wallet and Mint. Available at: https://github.com/cashubtc/nutshell
- Rizful Lightning Services. Available at: https://rizful.com
- NIP-17: Direct Messages. Available at: https://github.com/nostr-protocol/nips/blob/master/17.md
- NIP-59: Gift Wrap. Available at: https://github.com/nostr-protocol/nips/blob/master/59.md
- NIP-85: Trusted Assertions (Draft). Available at: https://github.com/nostr-protocol/nips/pull/85
- 0xChat: Secure Nostr Messaging. Available at: https://0xchat.com
- Brainstorm: Web of Trust Relay. Pretty Good Freedom Tech. Available at: https://github.com/Pretty-Good-Freedom-Tech/brainstorm
- Easy Onboarding Flow for Nostr Clients. Megalith Lightning Docs. Available at: https://docs.megalithic.me/rizful-tips-and-tricks/easy-onboarding-for-nostr-clients/